As terrorist networks attempt to adapt through coordination and relocation, Pakistan’s response is undergoing a transformation of its own, shifting from reactive operations to a broader, intelligence-driven strategy designed to dismantle threats across multiple domains.
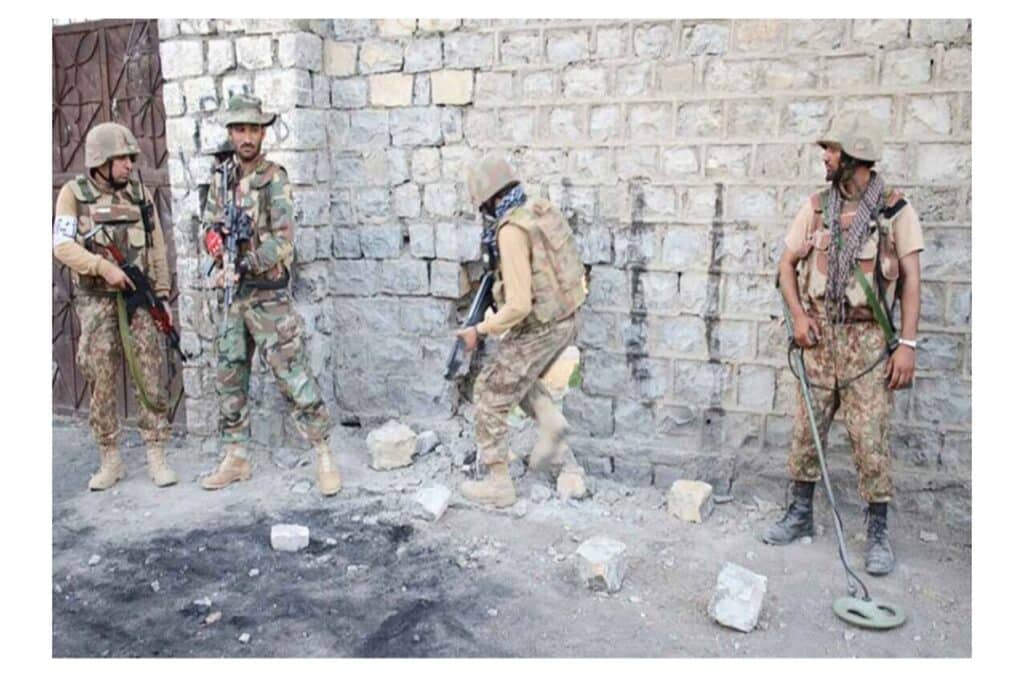
Recent operations in Balochistan and Khyber District highlight this evolution. Precision strikes, real-time intelligence monitoring, and rapid response deployments have enabled security forces to neutralize key targets, disrupt communication networks, and prevent planned attacks before execution.
In Panjgur, the elimination of a high-value commander and his network demonstrated the effectiveness of signal intercepts and coordinated targeting. In other districts, drone-assisted strikes and ground operations have further degraded operational capacity.
This approach reflects a shift toward predictive counterterrorism. Rather than waiting for attacks to occur, security agencies are increasingly identifying and neutralizing threats at the planning stage, reducing both frequency and impact.
At the same time, Pakistan continues to balance military action with diplomatic engagement. Regional coordination, including outreach to key partners, remains an essential component in managing cross-border dimensions of the threat.
Officials stress that the objective is not only to disrupt immediate threats but to deny terrorist networks the ability to regroup, communicate, and sustain operations over time.
While challenges persist, the cumulative effect of sustained operations, intelligence integration, and strategic coordination is placing terrorist networks under consistent pressure.
The emerging dynamic suggests a clear trajectory: as terrorist tactics evolve, Pakistan’s counterterrorism framework is evolving faster, expanding its reach, sharpening its precision, and reinforcing control across the security landscape.